Your Domain is being spoofed right now.
because you have no protection and are one spoofed email away from a client losing trust in you, or worse, wiring money to an attacker posing as your business.
Attackers are sending emails as your business, intercepting payments, scamming clients, and destroying the trust you've spent years building. ObaShield Layered Protection closes that gap permanently, in 48 hours.
Choose the plan that fits where you are. Every plan includes hands-on setup no DIY required.
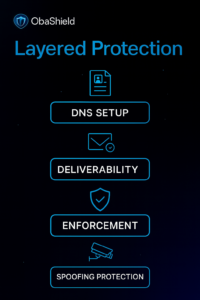
ObaShield Layered Protection
$497
One-time setup: includes 30-day onboarding
Best for: Solopreneurs, freelancers, and small teams sending under 5,000 emails per month.
What’s Included:
SPF configuration — stops unauthorized services from sending as your domain foundational configuration for domain authentication
Deliverability Optimization — ensure your emails reach inboxes, not spam folders
Enforcement — apply SPF, DKIM, and DMARC policies to block spoofing attempts
Spoofing Protection — monitor and prevent impersonation threats targeting your brand
Who It’s For: Small businesses and startups seeking fast, affordable protection with minimal setup.
ObaShield Identity Core
$149
per month · annual = $1,490 ($124/mo)
+ $297 one-time setup
Purpose: Maintain ongoing trust, visibility, and brand protection.
What’s included: Everything in ObaShield Layered Protection:
Continuous DMARC monitoring
Authentication drift detection
Domain reputation tracking
Brand impersonation alerts
Monthly trust score reviews
Who It’s For: Growing organizations that want continuous oversight and proactive protection.

ObaShield Guardian
$349
per month · annual = $3,490 ($291/mo)
+ $497 one-time setup
Purpose: Executive-level reporting you can actually use.
What’s Included: Everything in ObaShield Identity Core, plus:
XDR integration across email, endpoints, cloud apps, and identities
Attack‑chain correlation and visibility
AI‑driven threat detection
Automated disruption of active attacks
Compromised identity detection
Executive incident summaries and insights
Who It’s For: Organizations that want identity protection and full threat detection across their environment, a complete trust ecosystem.

